Retail stores are leading targets for after-hours break-in and burglary. Criminals are after cash, valuable merchandise and equipment. Not only does it cost a business thousands in lost assets, it can also leave buildings and premises with considerable damage. 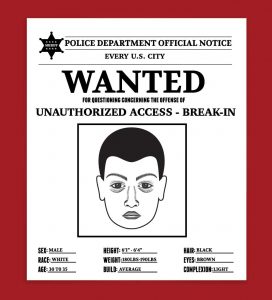
Who’s Responsible?
In our experience, burglaries are carried out by experienced criminals, often organized crime rings. They have likely committed similar crimes and are up-to-date on the latest security systems. Not only are the perpetrators sophisticated, they have access to special tools. It’s reasonable to assume that these break-ins have been carefully planned.
Lowering Risks for After-Hours Break-In and Burglary
You may ask yourself, “How can we lower our risk?” While you can’t prevent every incident, you can put security measures in place. Here are just a few basics to consider:
• Monitored security alarm systems
• Increased lighting indoors and outdoors
• Indoor / outdoor video surveillance
• Access control
How Do You Know Your Security System is Online and Functioning as Designed?
Even the most experienced retailers with state-of-the-art security systems have a difficult time knowing the answer to this question. The reality is, you can’t. Unless, of course, your security system is monitored 24x7x365 by a RMM (remote monitoring and management) tool.
What’s a RMM?
Remote monitoring and management (RMM) tools are also known as network management or remote monitoring software. It’s a type of software that has been designed to remotely and proactively monitor endpoints, networks and computers. The intent of the tool is to alert when there is a problem or potential problem.
Is There a RMM Specifically for Security Systems?
As a matter of fact, there is. Vunetrix Network Monitor(VNM) was purpose-built for physical security. The technology allows you to view your multi-vendor infrastructure through a single dashboard. By deploying the VNM, Security professionals can gather insights about their security system. They know if and when there is a problem. Best of all, Security teams can respond instantly, sometimes catching perpetrators in the act.
We like to say, “Vunetrix makes the invisible, visible.”
For more information about VNM and how it can help Security professionals just like you, take a look at our case study
